December 15, 2020
Know Your Customer (KYC) and screening are crucial steps while building your e-wallet solution. This is essential, as it serves financial institutions to verify whether their customer is a living person, and to avoid fraud. For those who are considering developing an e-wallet banking app, we’ve put together some valuable insights from our own experience in building e-wallets.
Security measures in a rapidly expanding market
In 2017 just 5% of the British population was using e-wallets. The UK was the 4th in the world, China being the leader with around 36% of e-wallet users among their population. It is projected that by 2022, 20% of the global population will use e-wallet services.
The increased ease with which e-money circulates in the global economy is a double edged sword. It enables all kinds of bad actors—fraudsters, drug cartels or even terrorist cells—to hide illegally obtained funds in plain sight. The amount of globally laundered money is about 2 – 5% of global GDP in one year (report of the United Nations). And the report of the Financial Conduct Authority (FCA) stated that at least £100bn was laundered through the UK alone. The need for efficient and constructive anti money-laundering measures is imperative for authorities all over the globe.
In the context of e-wallets, those regulations usually fall under the umbrella terms of Anti-money Laundering and Counter-Terrorism Financing (AML/CFT) compliance. Even though specific regulations differ between jurisdictions, they can be generalized into two main groups of measures:
- (Electronic) know your customer (eKYC) is the obligatory (remote) verification of each new customer identity at sign-up, probing deeper over time if the user wants to for example unlock new transaction limits or store more funds on an account.
- Screenings are based on cross checking the customers’ identities against sanctions lists of individuals or entities known as related to criminal activities, terrorist funding or even being politically exposed (thus highly susceptible to corruption and money-laundering activities).
(Electronic) know your customer (eKYC)
The goal of the eKYC process is to identify the customer of the e-wallet application and therefore to be able to validate customer-related risks.
eKYC is not only a crucial part of AML/CFT compliance, but also helps to mitigate risks and liabilities down the road (eg. having a verified customer data is essential for successful debt collection). It is therefore a standard procedure for financial institutions, and is also applicable for e-wallets.
Regulatory frameworks require financial institutions to apply spending limits on unverified users. There are several thresholds of verification. Completing each of them gives the user access to higher limits of the account balance, top-up and online payment values. Those limits can vary depending on jurisdictions but also the risk appetite of the institution opening the accounts (usually a bank).
How is customer identity validated? Basic validation is usually incorporated into the sign-up process. It may cover:
- Phone number verification
- Scanning the user’s ID during sign-up to validate the data provided in the sign-up form
- Liveness check
The IDs scanned by the customer are verified in order to rule out:
- ID formats and types non-existent in the declared country
- Expired IDs
- Manual modification of IDs (e.g. image correction)
- Invalid checksums of the ID number (which may occur in fake IDs)
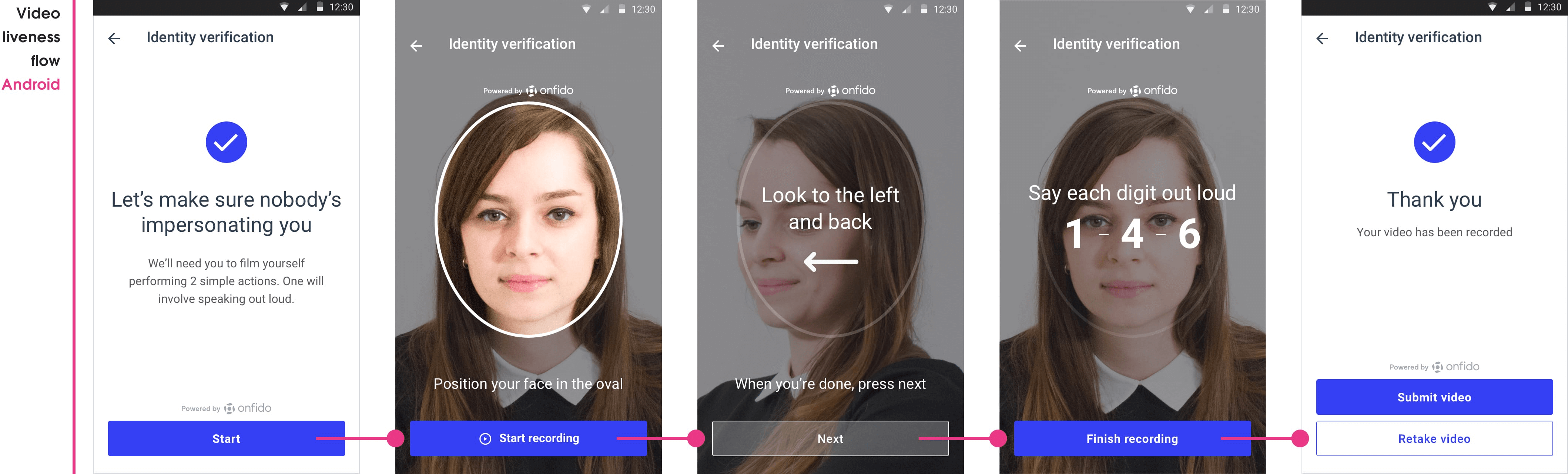
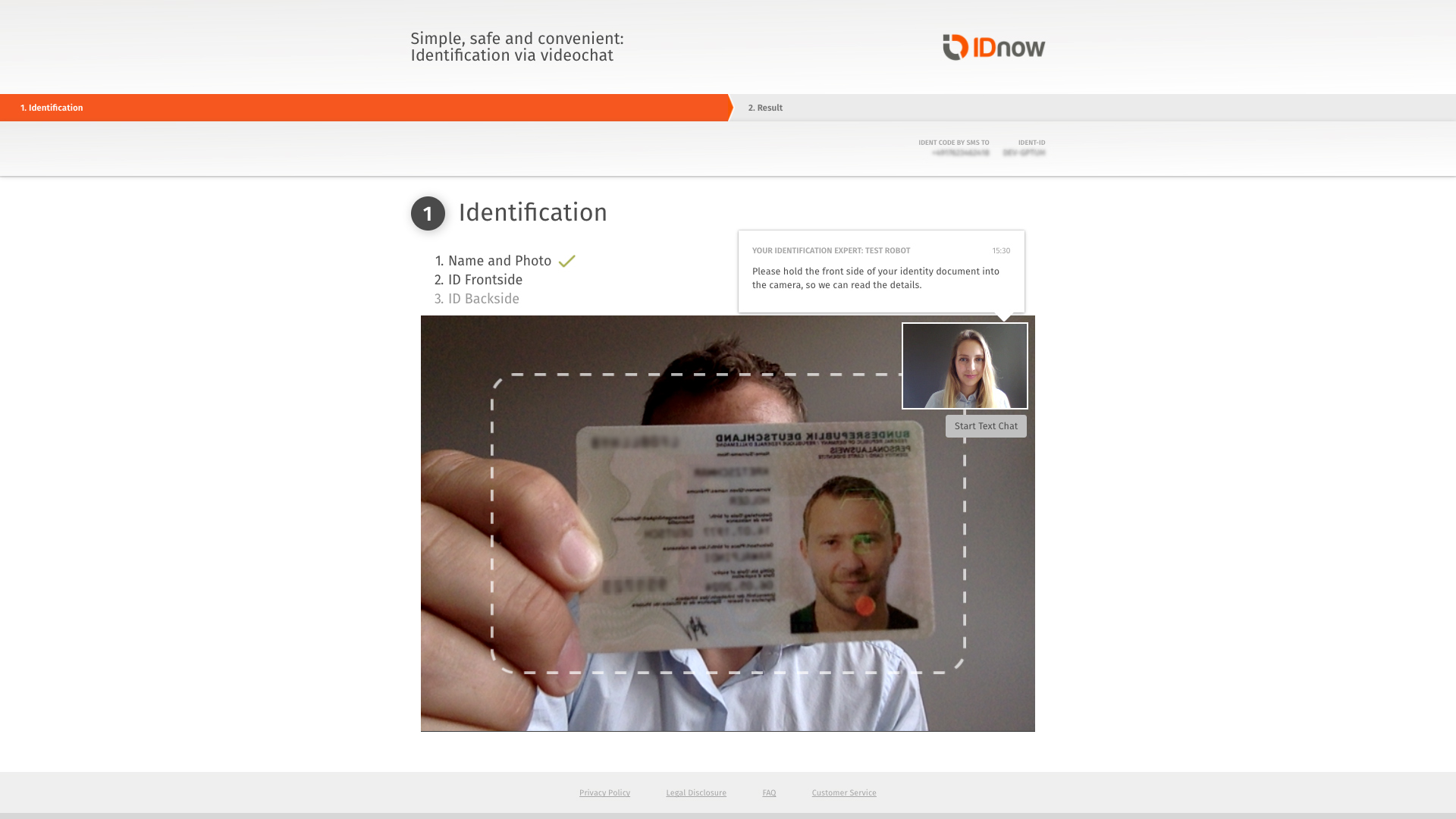
Biometric verification of the scanned documents and the person performing the eKYC process is usually key. For additional security liveness detection might be used to verify the user’s presence. Liveness detection usually tries to detect if a person is performing actions, like blinking, making facial expressions which makes it more difficult for a fraudster trying to impersonate someone else.
Using trusted 3rd party providers to perform most of those checks and processes is usually a given. These providers use a number of measures to eliminate spoofing attempts, particularly the use of masks, still photos, pre-recorded videos and other attempts at cheating one’s way through the user verification process.
Caution though, when choosing the KYC provider take into account your target jurisdiction. Even when operating within the same legal framework (ie. EU) interpretation can vary from country to country. For example, even though operating under the same EU directives, regulators in Germany (BAFIN) don’t allow liveness checks performed solely by AI algorithms. Whereas in the Netherlands (AFM) or UK (FAS) AI checks are considered sufficiently secure. Hence when developing a service in Germany one would rather go with providers offering a verification call (IDnow or WebID) compared to other jurisdictions where AI-based services like Onfido or Jumio should be enough.
Based on transaction limits, KYC can be a multi-level process that implements more detailed checks as the limit gets higher. Once a user’s identity is verified, their risk can be assessed.
Sanctions lists and user screenings
Sanctions lists enumerate individuals, groups and organisations involved in criminal activities such as terrorism, money laundering, drug trafficking, human rights violations and more. There are thousands of local and global screening lists compiled by states and organizations such as Interpol or the UN.
Another form of screening are PEP list checks. PEP or a Politically Exposed Person is one who is or has been entrusted with a public office or function. All such people require financial services but are, at the same time vulnerable to financial crimes like corruption and money laundering. The financial services sector, therefore, classifies them as higher risk clients and implement the necessary PEP compliance measures to protect themselves from being implicated in such crimes.
In order to protect an e-wallet service from being used for criminal activities, and to protect oneself from painful fines, e-wallet providers need to perform thorough screenings of each user.
The sanctions list screening is limited, and only possible via a number of third-party providers. It is an automated process of scanning sanctions lists, with results available within seconds.
The results take the form of a list of records with matching strength. The more user data provided, the better the matching strength. Basic matching requirements are the name, surname, country, and date of birth.
The matched records provide details about the user such as type of record (financial crime category, PEP, banned countries, others) and reference information (e.g. police notes, press clippings, etc).
Recurring verification
KYC and screening is not a process only relevant during customer onboarding. While new KYC steps follow with each transaction threshold, screenings against sanctions lists should be repeated regularly, as an existing customer could appear on one of the sanctions lists.
If the KYC process is interrupted by the customer’s failure to comply with the requirements, if a new level of KYC verification reveals inconsistencies in user data, or if a screening provides a valid match, a downgrading or blocking procedure must be initiated and in some cases, the appropriate authorities must be informed.
Customer risk assessment - other measures
What other measures must be taken to control risk associated with e-wallet users? There is a long list of good practices and legal requirements that differ from regulator to regulator. Never underestimate the significance of keeping up with regulatory changes.
Here are several measures that can be taken to improve risk management and prevent criminal activity:
- Track transaction patterns to detect symptoms of criminal activity
- Track transactions involving high-risk users
- Maintain records of high-risk users’ activities
- Find ways to detect multiple connected actions performed by different users - such as multiple account registrations or transfers that seem connected
- Track recurring transactions just below the next threshold
How does this affect the user experience?
eKYC and conversion
Time-consuming eKYC in the early stages of the customer onboarding process may be a killer for the sign-up conversion. It is key to adjust your KYC verification methods to the potential risks and their severity. In plain words: adjust your requirements to the transaction limit threshold.
The right wording of prompts and notifications can facilitate conversion. Pay attention to your microcopy. Customers need to understand why they need to share their personal information and how it will be processed. They will not be willing to share sensitive information if the context is unclear.
Screening troubleshooting
Despite battle-tested algorithms and flexible KYC processes, automated verification can still result in a false negative or a false positive.
While a false negative result may lead to some criminal activities performed through an e-wallet service, it is likely to be verified and made right in another screening round or caught thanks to transaction monitoring and other risk control measures mentioned above. As for potential legal vulnerability and fines, it is most important to make sure that the false negative was not due to an error in your data processing and identity verification process.
A false positive, however, is when an honest user is flagged as a match with a sanctions list. That can result in user frustration as it leads to situations such as:
- Blocking access to funds deposited in the e-wallet
- Blocking access to the multicurrency wallet during a private or business trip
- Suspending recurring payments for subscriptions
Again, communication and giving priority to solving such issues is a key factor in retaining users in the rapidly growing and increasingly competitive e-wallet market.
What’s next?
Customer risk assessment is not the only thing that should be executed perfectly while developing an e-wallet app. We have been active in the industry since 2014 and our expertise covers all aspects of building a successful e-wallet app: from legal requirements to go-to-market strategy. Interested in building your own e-wallet and looking for a trusted partner? Don’t hesitate to reach out to us!
For more about e-wallets or fintech - check out our blog!
At YND we help companies successfully develop products across various industries: from mobile payment, finance management, travel booking to E-commerce. In need of some brain power? Reach out to us via hello@ynd.co with questions about your projects.
